How the HITRUST Threat Catalogue delivers deeper value for your risk assessment
Your organization may already be reaping the benefits of the HITRUST® CSF framework to ensure the safety of vital data. The framework relies on and integrates multiple standards to provide a trusted foundation for your information security controls.
Given the escalation of cyberthreats and the potential for significant data and privacy loss from data breaches, the need for controls addressing specific threats to your information assets is especially critical now.
However, because some control frameworks are relatively static and not regularly updated, they have limited value in reflecting new and emerging threats. That’s where the HITRUST CSF along with HITRUST Threat Catalogue can help.
The threat catalogue was designed to assist organizations with their information security by aligning cyber threats with HITRUST control requirements in the most comprehensive manner possible. The HITRUST Threat Catalogue helps organizations better understand and mitigate threats to sensitive information by supporting the risk and threat analysis processes and alleviate some of the burden and expense associated with this level of analysis
The explicit alignment of threats to the HITRUST CSF produces more detailed and accurate results compared to other existing threat catalogues. In fact, the most recent version of the HITRUST Threat Catalogue has been updated to include new guidelines from the Cybersecurity and Infrastructure Security Agency (CISA) and other reputable industry sources to help better address ransomware attacks.
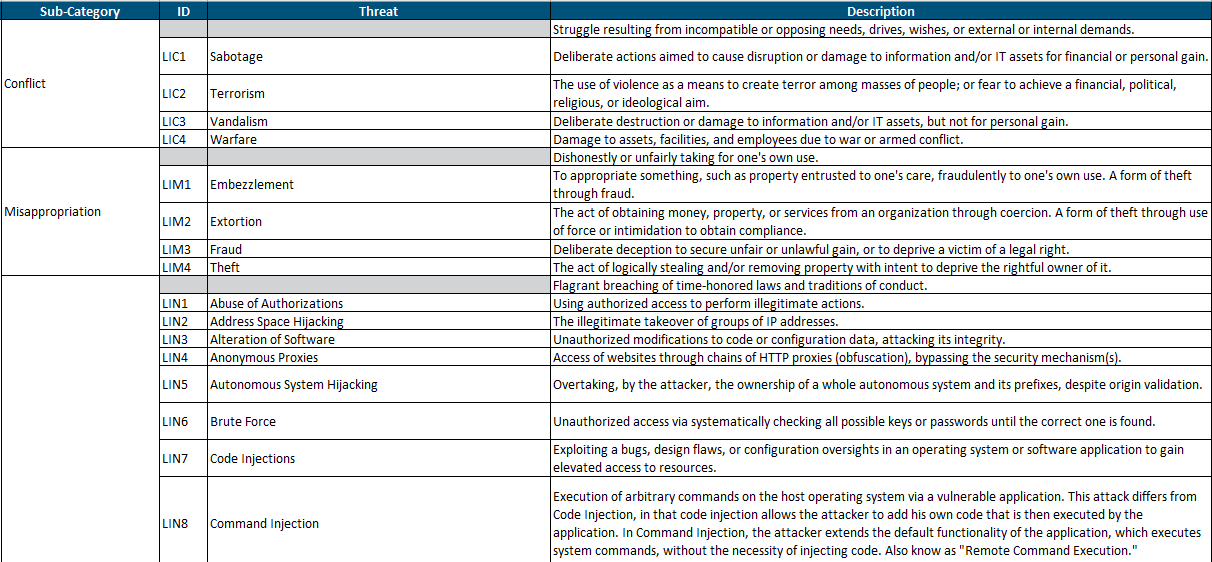
A sampling of threats from the HITRUST Threat Catalogue.
What exactly is a HITRUST Threat Catalogue?
It’s one of the resources provided by HITRUST as part of their risk analysis approach. The threat catalogue improves risk management by increasing visibility into cybersecurity threats that target sensitive data such as protected health information (PHI) and other personally identifiable information (PII). The threat catalogue also categorizes the specific controls required to address these threats:
- Logical: This category in the HITRUST Threat Catalogue focuses on all IT-related assets, including but not limited to software systems, data and networks. Because this category contains a large number and variety of threats, using the catalogue to inventory and categorize risk is beneficial for any organization developing cyber-defense programs.
- Organizational: Compliance with various contractual, regulatory, legal and other requirements is addressed in this category of the HITRUST Threat Catalogue. Despite having the fewest number of threats, this category is regarded as critical, since noncompliance with regulations can result in massive financial costs to a business in the form of regulatory fines and damaged reputation.
- Physical: This threat category in the HITRUST Threat Catalogue focuses on both intentional and unintentional damages, such as natural disasters and man-made threats.
What are the main benefits of the HITRUST Threat Catalogue?
- Provides a collection of “reasonably anticipated” threats that are spelled out at a corresponding HITRUST CSF control level.
- Allows healthcare and other organizations using the HITRUST CSF framework to concurrently conduct multiple types of risk analyses. For example, it’s ideal to address HIPAA security regulations regarding risk analysis. However, it could also be used to demonstrate compliance with other risk management requirements where sensitive information such as PII and electronic protected health information (EPHI) is involved. Insurance companies, billing companies and healthcare systems themselves will find a great benefit from the catalogue.
- Helps you understand threat advisories and your control coverage and the resulting level of risk.
- Since HITRUST updates the threat catalogue and HITRUST CSF, you can be confident in the relevancy and currency of cyber defenses by using both to manage your information security program.
Specific threats are mapped to HITRUST CSF framework controls.
First released in 2018, the HITRUST Threat Catalogue was updated last year to begin mapping ransomware threats to HITRUST controls, making it more relevant and easier to use than ever. These mappings help with incident response, decision support and other risk mitigation controls. Building on content and concepts in the current Threat Catalogue, HITRUST has an important Risk Catalogue initiative underway that will significantly change how threat information can be leveraged by HITRUST Organizations.
The HITRUST Threat Catalogue is a comprehensive tool for implementing the right control for a particular risk faced by your organization. It helps keeps your operations secure and offers confidence to all your stakeholders.
How Wipfli can help
Wipfli professionals have deep experience helping clients navigate the HITRUST CSF. We can help you leverage the HITRUST Threat Catalogue to deploy effective controls to shore up your cyber defenses. Learn more about HITRUST certification assessment services.
Sign up to receive additional security and risk mitigation information in your inbox, or continue reading on: